You don’t want that someone is calling your Azure Functions unauthenticated. You can rely on old-school function keys or use Azure Active Directory. Azure Functions provide elegant Authentication / Authorization functionality previous known as Easy Auth which works nicely with Azure API Management.
Setup the Azure Function to Use Azure Active Directory
The first thing you need to do is to enable Authentication / Authorization in Platform Features.


Do not forget set Action to take when request is not authenticated to Login in with Azure Active Directory otherwise the function can be still called anonymously.
Next you need to register your application in the Azure Active Directory. For this demo we create new application registration.

When you are finished it could looks to similar to this.

To be sure it really works call the function with some REST Client and the status code must be 401 Unauthorized.
HTTP/1.1 401 Unauthorized
Content-Length: 58
Content-Type: text/html
WWW-Authenticate: Bearer realm="testazurefunctionapp20200415114430.azurewebsites.net" authorization_uri="https://login.windows.net/40a85801-c1db-488a-812e-b788c880f22c/oauth2/authorize" resource_id="edce07520-ed35-4a3e-9d37-31bd5d3d6a7e"
Date: Wed, 15 Apr 2020 14:35:06 GMT
Connection: close
You do not have permission to view this directory or page.
Configure Azure API Management
First you need to enable managed identity. This allows API Management to get JWT Token to access Azure Function.

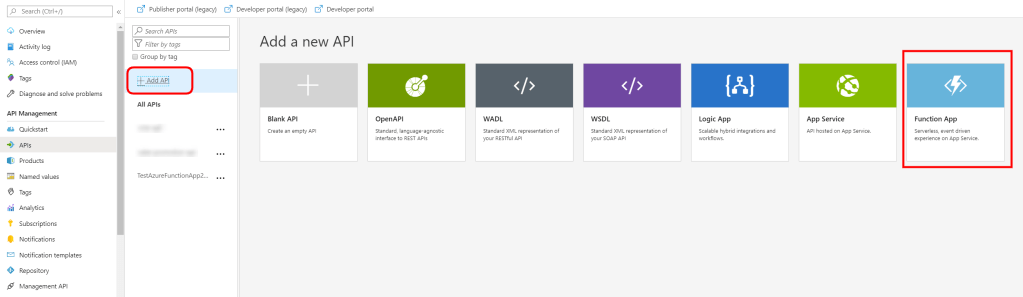
Now you can add new API.
Finally you need to add a new authentication-managed-identity inbound policy. As a resource you set Application ID of the application created within Azure Function Authentication / Authorization in previous steps. You can find this in Azure Active Directory Enterprise Applications blade.
<policies>
<inbound>
<base />
<authentication-managed-identity resource="edce07520-ed35-4a3e-9d37-31bd5d3d6a7e" />
</inbound>
<backend>
<base />
</backend>
<outbound>
<base />
</outbound>
<on-error>
<base />
</on-error>
</policies>
After this you can call your Azure Function from Azure API Management.

You concentrated it on the essentials and put it in a nutshell!
LikeLike
Anton Kalcik, Before All, Thanks for this information, very useful, i leave you with a question,¿what about giving the access only a one managed Identity?
so what i want is: i have an API, that can access to the Azure Function using Managed Identity, but only just one Managed Identity, i dont see that we can specify wich Managed Identity can access to the Azure Function.
LikeLiked by 2 people
This is the best information I’ve found on this subject. After messing around with this stuff for 2 days, trying to follow the Microsoft documentation, I finally found this site. Everything finally makes sense, and it’s so simple.
Thank you for sharing this information!
LikeLike
Thanks Anton, your answer corrected that given on docs.microsoft.com ;)
LikeLike